 Your new post is loading...
 Your new post is loading...

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
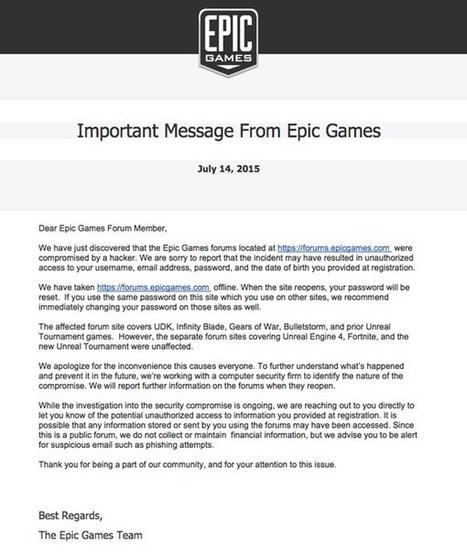
If you're an avid video gamer, chances are that you know of Epic Games. They're the developers of popular games such as Infinity Blade, Gears of War, Unreal Tournament… and – if you’re as old as me – you might even remember their founder Tim Sweeney’s classic DOS era shareware gameZZT.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Phishing

|
Scooped by
Gust MEES
|
HOW TO PROTECT YOURSELF AGAINST PHISHING SCAMS Given the wide variety of phishing attacks, it is important that we all know what to do when we come across what we suspect might be a phish. Hence, here are a few suggestions for how you can protect yourself against these phishing attacks.
Learn more:
- http://www.scoop.it/t/21st-century-learning-and-teaching/?tag=Phishing

|
Scooped by
Gust MEES
|
Gezielte, gut getarnte Phishing-Attacken sind große Gefahr für Unternehmen.
Der Security-Software-Hersteller ESET rät Unternehmen zu einer verstärkten Sensibilisierung für Phishing-Attacken und damit einhergehend zu einer besseren IT-Weiterbildung. Nur so können die eigenen Mitarbeiter vor gezielten und gut getarnten Angriffen geschützt werden. Denn Attacken dieser Art sind mittlerweile geschickt auf ihre Zielgruppen zugeschnitten und nur mit großer Sorgfalt und Verständnis erkennbar.
Anlass für den Ratschlag ist das Ergebnis eines Tests, den das Center of Excellence for Research, Innovation, Education and Industrial Labs Partnership (CEFRIEL) im Auftrag von 15 internationalen Unternehmen kürzlich durchführte. Die Einrichtung prüfte die Anfälligkeit von Mitarbeitern für speziell auf Unternehmen gemünzte Betrugsversuche, so genannte „Spear-Phishing“-Attacken. Das Ergebnis: Jeder Fünfte ging den Testern ins Netz.
Learn more:
- http://www.scoop.it/t/securite-pc-et-internet/?tag=Phishing

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
In a recent YouTube video, software company Venafi reveals that PayPal phishing attacks are taking advantage of users' trust in wildcard certificates.
Learn more:

|
Scooped by
Gust MEES
|
A typical chain letter consists of a message that attempts to convince the recipient to make a number of copies of the letter and then pass them on to as many recipients as possible.

|
Scooped by
Gust MEES
|
Phishing is the act of attempting to acquire information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, banks, online payment processors or IT administrators are commonly used to lure unsuspecting public.

|
Scooped by
Gust MEES
|
We talk about phishing a lot on SecurityWatch. While we regularly warn readers to not fall for phishing scams, it got us thinking: how many people know how to recognize a phishing scam?
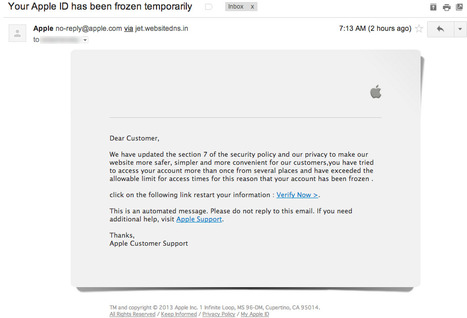
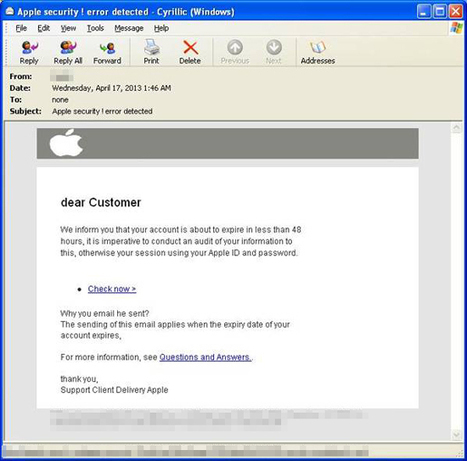
Apple users have reported receiving phishing emails entitled “Your Apple ID has been frozen temporarily,” which attempt to trick recipient... If you come across such emails, you can report them to Apple by forwarding them to reportphishing@apple.com. If you’re already a victim of this scheme, take the appropriate measures depending on what information you’ve handed over to the scammers.
Steps may include changing passwords, and keeping a close eye on your bank account in case you’ve provided financial details.

|
Scooped by
Gust MEES
|
Human Factors and Ergonomics Society mission is to promote the discovery and exchange of knowledge concerning the characteristics of human beings that are applicable to the design of systems and devices of all kinds. The author of a paper to be presented at the upcoming 2013 International Human Factors and Ergonomics Society Annual Meeting has described behavioral, cognitive, and perceptual attributes of e-mail users who are vulnerable to phishing attacks. Phishing is the use of fraudulent e-mail correspondence to obtain passwords and credit card information, or to send viruses.

|
Scooped by
Gust MEES
|
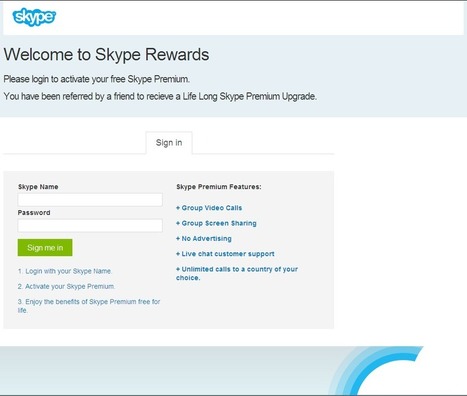
Our researchers discoveres a scam being spread via Skype that is designed to steal the log in credentials for Skype users by dangling free premium upgrades
Phishers appear to have concentrated their fire on a relatively new target: Apple IDs.
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Online security companies have been making their predictions for 2015, from the malware that will be trying to weasel its way onto our computers and smartphones to the prospect of cyberwar involving state-sponsored hackers.
Here’s a summary of what you should be watching out for online in 2015, based on the predictions of companies including BitDefender, KPMG, AdaptiveMobile, Trend Micro, BAE Systems, WebSense, InfoSec Institute, Symantec, Kaspersky, Proofpoint and Sophos. The links lead to their full predictions.
Read more: http://uk.businessinsider.com/beyond-phishing-experts-predict-the-cybercrime-of-2015-2014-12?utm_content=bufferbd004&utm_medium=social&utm_source=twitter.com&utm_campaign=buffer?r=US#ixzz3N3npIVff

|
Scooped by
Gust MEES
|
Cyber Monday is a feeding frenzy for hackers looking to exploit businesses and consumers. Here's how to safeguard your sensitive information.

|
Scooped by
Gust MEES
|

|
Scooped by
Gust MEES
|
Apple phishing scams are not uncommon, but phishing pages hosted on the website of a major company are certainly worth looking at. Experts have found ...
“The mere presence of old software can often provide sufficient incentive for a hacker to target one system over another, and to spend more time looking for additional vulnerabilities or trying to probe deeper into the internal network.”
The problem with phishing pages hosted on the web servers of reputable companies is that it’s less likely that they’ll be flagged. Furthermore, some users might be tricked into thinking that the pages are legit considering that they’re on a trusted domain.
In this case, the attackers could have made up a story about a collaboration between EA and Apple and that would have truly made the phish efficient.

|
Scooped by
Gust MEES
|
Phishing is the act of attempting to acquire information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity in an electronic communication. Communications purporting to be from popular social web sites, auction sites, banks, online payment processors or IT administrators are commonly used to lure unsuspecting public.

|
Scooped by
Gust MEES
|
With cloud infrastructure easily scalable and rented botnets coming on the cheap, the cost of conducting massive phishing campaigns continues to decline for cybercriminals.
Employees of Missouribased Saint Louis University fell victim to a phishing email that resulted in them providing account information, subsequently putting thousands at risk. How many victims? More than 3,200 individuals were impacted. What type of personal information? Names, Social Security numbers, direct deposit information and personal health information, including diagnoses, procedures and medical chart information.

|
Scooped by
Gust MEES
|
Transcription de l' infographie : L'hameçonnage : combien de personnes en sont victimes?

|
Scooped by
Gust MEES
|
The latest figures from the APWG show a decline in phishing reports. Verizon, on the other hand, implies that almost all incidents of cyber espionage reported in the last year included some phishing... An academic study into human susceptibility to phishing has found that 92% of people misclassify phishing emails, despite efforts to educate people about the dangers. Educating users to keep a wary eye out for phishing attempts has been a major focus for security admins and providers, but it seems like the bad guys are managing to keep ahead of the curve.

|
Scooped by
Gust MEES
|
A group of children in Alaska took over their classroom computers after phishing account details from teachers. They asked teachers at Schoenbar Middle School, for 12 to 13-year-olds, to enter admin names and passwords to accept a false software update, according to reports.
|



 Your new post is loading...
Your new post is loading...





![Phishing Deceives the Masses [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bpENVbKlv4q8nU8YQXp8jDl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)














![L'hameçonnage : combien de personnes en sont victimes? [Infographic] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/OXS9mYQx_J1s-8GXqYb4Gjl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)







Learn more / En savoir plus / Mehr erfahren:
http://www.scoop.it/t/securite-pc-et-internet/?&tag=Phishing
http://www.scoop.it/t/21st-century-learning-and-teaching/?&tag=Phishing