An infographic from security-testing company Veracode explores the rise of data breaches and what it could mean for businesses and consumers.
Get Started for FREE
Sign up with Facebook Sign up with X
I don't have a Facebook or a X account

 Your new post is loading... Your new post is loading...
 Your new post is loading... Your new post is loading...
Current selected tags: 'BYOD-Dangers', 'eLearning'. Clear
OpenDNS and the Ponemon Institute teamed up to create a unique infographic that provides statistics on one of the most concerning topics in the industry.
Gust MEES
Please check my FREE courses and curations here to get smart and don't forget "Forewarned is Forearmed"!
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
- http://gustmees.wordpress.com/category/get-smart-with-5-minutes-tutorials/
- http://gustmeesen.wordpress.com/2012/03/16/beginners-it-security-guide/
- http://www.scoop.it/t/ict-security-tools
- http://www.scoop.it/t/securite-pc-et-internet
- http://www.scoop.it/t/apps-for-any-use-mostly-for-education-and-free
===> Be aware of the malware!!! <===
Read more: http://www.scmagazine.com/mobile-security-stats/slideshow/805/#0
Lisa Nielsen, the author of "Teaching Generation Text: Using Cell Phones to Enhance Learning" and "The Innovative Educator" blog, believes it is time to shatter a few myths about students bringing their own devices (BYOD) to school.
Organizations that do not invest in security education for their employees put themselves at risk.
Gust MEES: when working with ICT Education of employees is a MUST, in Business and especially in Education while working with "Bring Your Own Device" (Hashtag on Twitter = #BYOD)!
Don't forget that Internetsafety alone isn't enough! You need also to protect the computer and other devices of "Bring Your Own Device" (BYOD), check my FREE courses here:
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
National Cybersecurity Awareness Month Advocates Good “Cyber Hygiene”
- http://gustmees.wordpress.com/2012/07/11/cyberhygiene-hygiene-for-ict-in-education-and-business/
- http://gustmees.wordpress.com/category/get-smart-with-5-minutes-tutorials/
- http://www.scoop.it/t/apple-mac-ios4-ipad-iphone-and-in-security
- http://www.scoop.it/t/ict-security-tools
- http://www.scoop.it/t/securite-pc-et-internet
Check out also "Security Education Services" from Trustwave:
Read more:
|
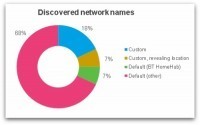
Do you always turn WiFi off on your smartphone before leaving the house or work? You might think there's no harm in having WiFi turned on but not connected to a network, but that's not necessarily the case.
A wireless device goes through a discovery process in which it attempts to connect to an available wireless network. This may either be ‘passive’ - listening for networks which are broadcasting themselves - or ‘active’ - sending out probe request packets in search of a network to connect to.
Most devices use both passive and active discovery in an attempt to connect to known/preferred networks. So it's very likely that your smartphone is broadcasting the names (SSIDs) of your favourite networks for anyone to see.
===> An ‘evil twin’ attack could even accomplish this without needing any knowledge of your WiFi password - very damaging for all of those who use mobile banking for instance! <===
Gust MEES: a MUST READ for anyone using m-Learning + "BYOD" and also any smartphone user...
Here are the most important aspects of BYOD to consider before implementation.
Gust MEES: check out also my FREE course about it here
- http://gustmees.wordpress.com/2012/07/07/bring-your-own-device-advantages-dangers-and-risks/
Read more. a MUST: http://www.fedtechmagazine.com/article/2012/08/5-takeaways-cio-councils-byod-toolkit
|



![Why You Should Care About Mobile Security [INFOGRAPHIC] | 21st Century Learning and Teaching | Scoop.it](https://img.scoop.it/bCDzCBQu4qMgWJAbygdm2jl72eJkfbmt4t8yenImKBVvK0kTmF0xjctABnaLJIm9)