By now, most everyone has heard the story: on April 23rd, the AP’s twitter account was “hacked.” The tweet, which was a fairly obviously fake, still managed to send Wall Street into a panic. The Dow Jones Industrial Average dropped 145 points in 2 minutes.
So why is this important? It highlights the reality of the threat landscape.
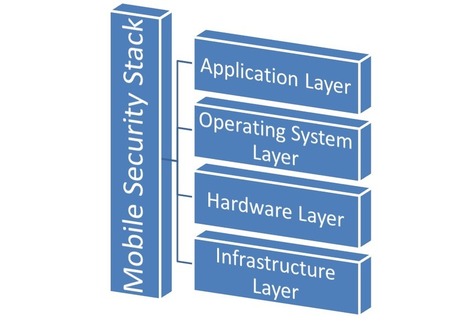
The point of the story is that mobile security isn’t just about protecting you from viruses. Threats don’t only come in the form of malicious applications that one inadvertently “sideloads” onto his or her device. Mobile security is also about making sure your data is protected.
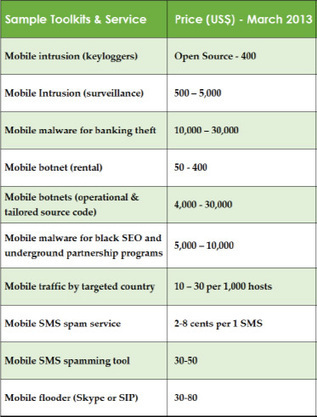
It doesn’t matter whether the economic climate is good or bad, there is always a market for fraud. The marketplace for carding is growing and will continue to grow. And as the engineers behind these types of attacks get smarter and smarter, we can only expect to see them more and more often.



 Your new post is loading...
Your new post is loading...















Learn more:
- https://gustmees.wordpress.com/2014/11/25/digital-citizenship-social-media-and-privacy/
- https://gustmees.wordpress.com/2014/11/18/why-cybersecurity-starts-at-home-and-is-concerning-all-of-us/